Hey there,
First of all I really appreciate everyone who took the time to attempt the puzzle. I’ve learned that it was probably a bit too cryptic or vague. So again, I thank everyone who took a crack at it.
The Puzzle:
Here’s the puzzle as it appeared in the blog post
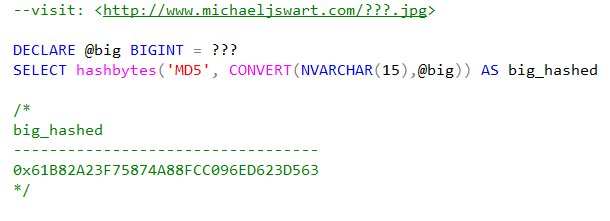
A puzzling situation (my T-SQL Tuesday entry). This entry is an actual puzzle. Here I’m asking you to do the impossible (or at least the computationally difficult). Solve for ???:
Solution next week.
BTW, Don’t even try to attack this using a brute force approach. Even if you could test 1000 values a millisecond it would take like a whole decade to crack it.
A Couple Hints
So yesterday I posted a couple hints. The first one said to look to the source for a clue. If you looked in the html source of the original puzzle page, you would find the following:
< !-- hey hey hey!!! good for you looking at the source and everything. As a reward for your attempt at resourcefulness, I'll remind you that this decade has two leap years -- >
The other hint I gave was that the puzzle is not about cryptography, but can be solved with one or two lines of T-SQL.
The Solution:
What I was hoping for is that most people would think that the warning against trying brute force was a comment on the number of values possible for a BIGINT variable. As it turns out, if the solution was arbitrary or random and if you use brute force to solve the puzzle at the rate I mentioned, it would take on average 300 thousand years to hit on the correct solution.
The big idea is that I’m telling you that it would take exactly a decade. See the following code:
DECLARE @big BIGINT, @now DATETIME, @in_a_decade DATETIME; SET @now = GETDATE(); SET @big = 1000000; SET @in_a_decade = DATEADD(YEAR, 10, @now); SET @big = @big * DATEDIFF(SECOND, @now, @in_a_decade); SELECT @big AS microseconds_per_decade, hashbytes('MD5', CONVERT(NVARCHAR ( 15 ) ,@big)) AS big_hashed /* microseconds_per_decade big_hashed 315532800000000 0x61B82A23F75874A88FCC096ED623D563 */ |
But That’s Not All
The puzzle, I posed had two instructions.
- The first was “Solve for ???”
- The second was the instruction: Visit https://michaeljswart.com/315532800000000.jpg
That gets you this image:

which is the next step. But that’s… another story.
The Winners
Brad Schulz was the first guy who followed the breadcrumbs to the end. Congrats Brad. An honorable mention goes to another blog reader who came up with the correct number for ???.
Where I Got The Ideas
- Well, the puzzle-as-a-scavenger-hunt idea came from Abstruse Goose who in turn probably got it from Google’s billboard puzzle.
- The key clue to solving the puzzle is that it takes a decade to solve. This idea was taken from an old book I once read called Puzzles in math and logic. (I think that book might still be in my parents house).
- A hint-in-the-source idea came from a now-defunct site called Puzzle Donkey.
- The rebus is a rebus and is a 400 year-old idea.





[…] Michael Swart comes up with a difficult puzzle of his own. Can you reverse-engineer an MD5 hash? You shouldn't, in theory, be able to do so (at least, easily), but here are some hints… And if you still can't figure it out, read the solution. […]
Pingback by Adam Machanic : T-SQL Tuesday #002: The Roundup — March 28, 2010 @ 3:58 pm